SYSTEMATIC REVIEW OF UAV SWARM RELAY NETWORKS AND FLYING AD HOC NETWORKS (FANETS)— PROTOCOLS, ROUTING CHALLENGES, SECURITY ASPECTS
DOI:
https://doi.org/10.71146/kjmr634Keywords:
Unmanned Aerial Vehicles (UAVs), Flying Ad Hoc Networks (FANETs), Routing Protocols, Mobility Management, Network Security, Geographic RoutingAbstract
Background: Unmanned Aerial Vehicles (UAVs) relay nets and Flying Ad Hoc Networks (FANETs) have become effective facilitators of applications like disaster management, surveillance, smart transportation and military logistics. Compared to the conventional mobile ad hoc networks, FANETs are subject to extreme mobility, three-dimensional movement, intermittency, and use of limited onboard resources, which present a great challenge to routing reliability, network performance as well as security.
Objective: This paper would be a systematic review of the literature on the UAV relay networks and FANETs with emphasis on routing protocols, challenges related to mobility, performance analysis, and security threats and solutions.
Methods: The systematic review was performed based on PRISMA 2020. A wide literature search on IEEE Xplore, Scopus, Web of Science, ACM Digital Library, and Google Scholar revealed the presence of appropriate literature within the last five years (2012-2025). After screening and quality evaluation, 137 peer reviewed articles were found by carefully sifting through a plethora of literature. This was achieved through narrative analysis of data and it was backed by comparative tables and graphical illustrations.
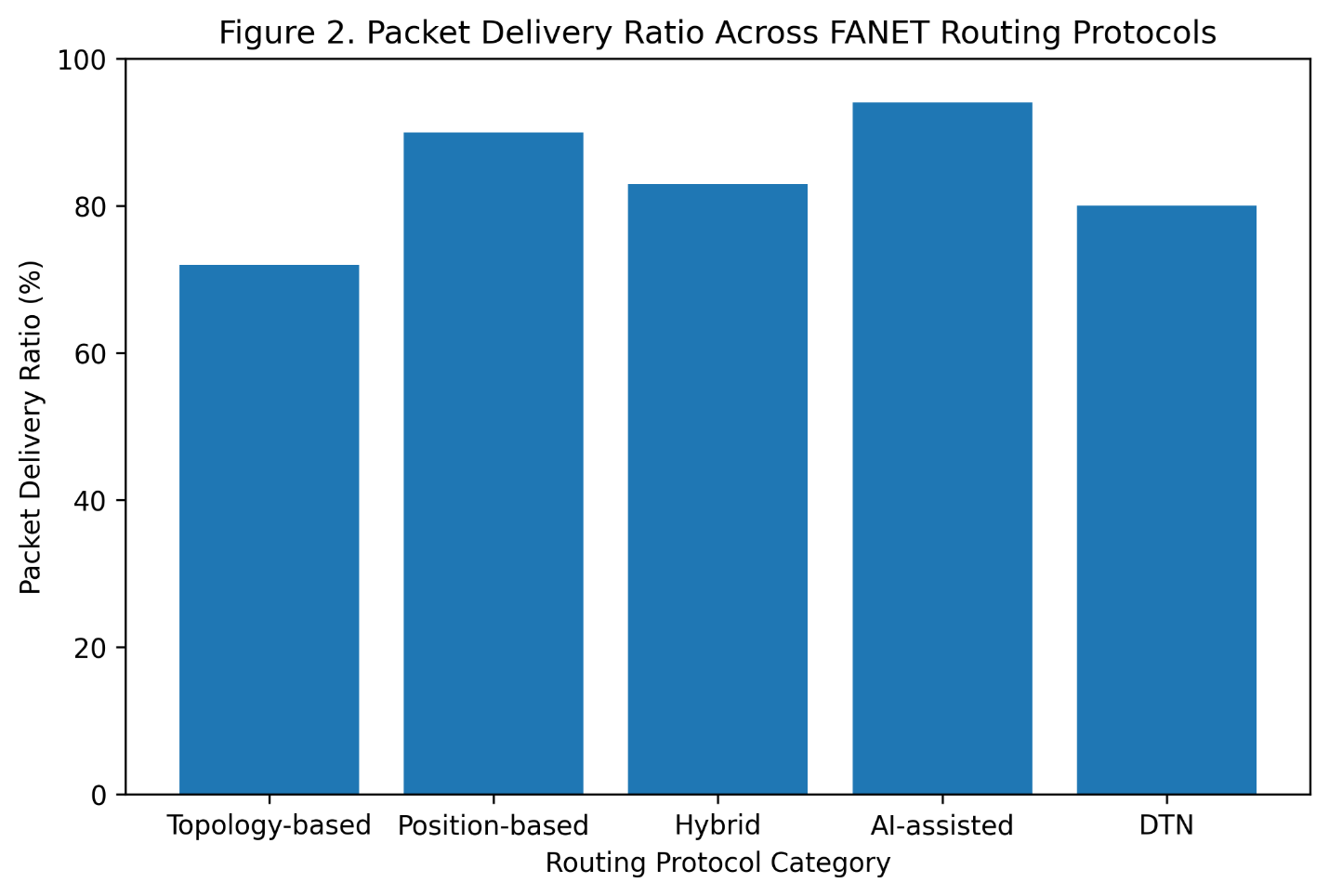
Results: The findings show that position-based (geographic) routing protocols always experience better packet delivery ratios (6595) and lower delay than topology-based routing protocols especially in high-mobility and dense FANET environment. As UAV speed is increased, breakages of links and poor routing stability increases, indicating the constraints of protocols which do not have mobility prediction mechanisms. Security analysis indicates that FANETs are susceptible to black hole attack which involves wormhole, GPS spoofing attack, Sybil, and denial of service attack. New countermeasures that take advantage of lightweight cryptography, trust-based routing, blockchain technology, and AI-based intrusion detection systems hold potential, but at the cost of energy consumption and algorithm costs still remain.
Conclusion: The conclusion of the review is that the performance of FANET is greatly affected by mobility dynamics, the choice of routing strategy, and security integration. The use of position-based and intelligent routing methods is more scalable and robust, and the security issue is still a research question. Future studies are needed on holistic, adaptive, and secure routing schemes, experimental studies, and cross-layer optimization to aid reliable large scale FANET implementations.
Downloads
Downloads
Published
Issue
Section
Categories
License
Copyright (c) 2025 Muhammad Asad, Waqas Rauf Khattak, Abdullah Shabbir, Waqar Ahmad (Author)

This work is licensed under a Creative Commons Attribution 4.0 International License.






